Introduction to SIP Scan
In the landscape of modern communications, the Session Initiation Protocol (SIP) powers most Voice over IP (VoIP) systems. As businesses and service providers increase their reliance on SIP infrastructure, the risk of security breaches grows in parallel. SIP scan refers to the process of systematically probing SIP-based networks and endpoints to identify vulnerabilities, misconfigurations, and unauthorized devices. For security engineers and penetration testers, SIP scan is a core technique in assessing VoIP security posture.
A robust SIP scan can reveal weak authentication, exposed SIP devices, and unpatched PBX systems. In 2025, with SIP-based telephony prevalent in corporate and cloud environments, leveraging SIP scan tools is essential for proactive defense. Popular open-source SIP scanner tools, such as SIPVicious, sippts, and SIPscan, enable security professionals to audit and secure their VoIP infrastructure efficiently.
Understanding SIP Protocol and VoIP Security
SIP (Session Initiation Protocol) is a signaling protocol widely used for initiating, maintaining, and terminating real-time sessions in VoIP, video, and messaging applications. SIP operates at the application layer, typically over UDP and TCP ports (default UDP 5060), and governs how endpoints discover each other, negotiate capabilities, and establish communication paths.
For developers building secure VoIP apps, understanding how to implement features like
callkit tutorial
on iOS or integrating aphone call api
is crucial for both functionality and security.However, the flexibility and ubiquity of SIP also make it a frequent target for attackers. Common vulnerabilities include:
- Weak or default authentication credentials
- Unrestricted SIP enumeration (user/extension discovery)
- Poorly configured PBX or SIP proxies
- Exposure of sensitive network information in SIP responses
- Lack of encryption for SIP signaling (allowing eavesdropping and manipulation)
SIP scan is critical because it uncovers these vulnerabilities before adversaries exploit them. Through automated SIP auditing, organizations can identify attack surfaces, enumerate valid extensions, and validate SIP device configurations. SIP scan is therefore a cornerstone in VoIP security strategies, helping mitigate SIP-based attacks such as toll fraud, spoofing, and denial of service.
How SIP Scan Works: Techniques and Methods
SIP Scan Methods
A SIP scan entails sending crafted SIP messages to targeted endpoints and analyzing responses. The main methods include:
- UDP vs TCP SIP Scans: SIP commonly uses UDP due to its low latency, but TCP is also supported. UDP scans are faster but may miss endpoints that only respond over TCP. Comprehensive SIP scan tools allow toggling between protocols.
- Port Scanning and Service Detection: Scanners probe common SIP ports (e.g., 5060, 5061) and attempt to identify active SIP services. This helps map the SIP infrastructure and locate devices.
- REGISTER, OPTIONS, INVITE Methods: SIP scan utilities send specific SIP requests:
OPTIONS: Used to check if a SIP endpoint is alive ("ping") and to gather supported capabilities.REGISTER: Tests whether endpoints accept registration attempts—useful for credential brute-forcing and enumeration.INVITE: Attempts to initiate a call, revealing active users or triggering call handling logic.
For teams building advanced VoIP features, integrating a
Video Calling API
or leveraging aVoice SDK
can enhance both security and user experience.Example: SIP Scan Packet Flow
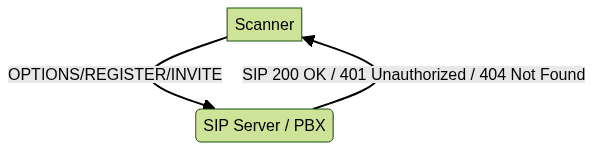
This interaction demonstrates how a SIP scanner sends crafted requests to the target SIP server. The response (OK, Unauthorized, Not Found) provides insight into available services, valid extensions, and potential vulnerabilities.
Popular SIP Scan Tools and Their Features
SIPVicious (svmap)
SIPVicious is one of the most widely adopted open-source SIP scanner suites. Its
svmap module is designed for scanning SIP endpoints on a network.Key features:
- Fast, multi-threaded scanning of IP ranges
- SIP service/extension enumeration via OPTIONS or REGISTER
- Flexible output formats (text, JSON)
If you're developing cross-platform VoIP apps, exploring
react native callkeep
can help you implement native call UI and call management, which complements SIP security practices.Usage example:
1python3 svmap.py -m OPTIONS 192.168.1.0/24
2Sample output:
1{
2 "host": "192.168.1.10",
3 "port": 5060,
4 "user-agent": "Asterisk PBX 18.0.0",
5 "status": "200 OK"
6}
7SIPVicious also includes modules for brute-forcing (
svcrack), fingerprinting (svwar), and registration attacks, making it a comprehensive toolkit for SIP penetration testing.sippts and SIPscan
sippts is a modular, open-source SIP penetration testing suite written in Python. It supports multi-threading and can audit both UDP and TCP SIP services.
Features include:
- SIP enumeration (users, extensions)
- Authentication brute-force
- Fuzzing and vulnerability checks
- Customizable SIP message templates
- Scans via UDP, TCP, or TLS
For those looking to add robust calling features to their apps, integrating a
phone call api
ensures seamless connectivity and compatibility with SIP-based infrastructures.Basic usage:
1python3 sippts.py -t 192.168.1.5 -m enum -p 5060
2SIPscan is another lightweight, multi-threaded SIP scanner focused on speed and efficiency for large-scale scans.
1sipscan --target 10.0.0.0/16 --method OPTIONS --threads 50
2Both tools support exporting results for further analysis, making them suitable for integration into security workflows.
Other Notable Tools: sipsak, sipsaker
sipsak is a command-line SIP testing tool for scripting and automation. It's ideal for service monitoring and basic SIP audits:
If you're interested in building secure VoIP apps for iOS, following a
callkit tutorial
can help you integrate native call management and enhance user trust.1sipsak -s sip:1000@192.168.1.20 -O
2sipsaker builds on sipsak, offering additional scripting and automation features, making it useful for continuous integration and SIP infrastructure monitoring.
Step-by-Step: Running a SIP Scan
Preparing Your Environment
Before running a SIP scan, ensure you have:
- Python 3.x (for most open-source scanners)
- Access to the target network or SIP devices
- Permission and legal authorization to scan (to avoid legal issues)
- Appropriate firewall rules to allow outbound/inbound SIP traffic
If you're developing VoIP solutions, consider reviewing a
callkit tutorial
to understand how to integrate secure and user-friendly call features on iOS.Running a Basic SIP Scan
Let’s walk through a basic scan using SIPVicious (
svmap):1python3 svmap.py -m OPTIONS 172.16.0.0/24
2To use sippts for user enumeration:
1python3 sippts.py -t 172.16.0.10 -m enum -u users.txt
2For SIPscan bulk scanning:
1sipscan --target 172.16.0.0/16 --method OPTIONS --threads 20
2When building or testing VoIP apps, integrating a reliable
phone call api
can streamline your development and ensure compatibility with SIP endpoints.Analyzing Results
SIP scan tools typically output response codes and device information. Common responses:
200 OK: Valid SIP endpoint or extension401 Unauthorized: Requires authentication (potential brute-force candidate)404 Not Found: Invalid extension or user486 Busy Here: Endpoint is busy/active
Parsing these responses helps identify valid users, discover SIP device types, and prioritize vulnerabilities.
Advanced Options
- Randomization: Randomize scan order to avoid detection using
--randomizeor equivalent. - Resuming Scans: Save scan state and resume interrupted scans with
--resume. - Scanning Ranges: Specify IP and port ranges for comprehensive coverage:
192.168.0.1-192.168.0.254:5060,5061. - Protocol Selection: Toggle between UDP, TCP, and TLS to audit all supported SIP transport layers.
For developers aiming to provide a seamless user experience, following a
callkit tutorial
ensures your VoIP app integrates smoothly with the device's native call interface.Best Practices for SIP Scanning and Security
- Ethical & Legal Considerations: Always secure explicit authorization before scanning production SIP infrastructure. Unauthorized SIP scans can disrupt services and may violate laws.
- Avoiding Service Disruption: Rate-limit scan speed, use non-intrusive methods (OPTIONS before REGISTER/INVITE), and monitor for call drops or false alarms.
- CI/CD Integration: Incorporate automated SIP scans into DevSecOps pipelines to catch misconfigurations before deployment. Use output in SIEM or ticketing systems for continuous monitoring.
Leveraging a
phone call api
and following best practices from acallkit tutorial
can help you build secure, scalable, and user-friendly VoIP solutions.Real-World Use Cases of SIP Scan
- Penetration Testing: Security teams leverage SIP scan tools to enumerate SIP devices, test for weak authentication, and assess exposure.
- VoIP Infrastructure Auditing: Regular SIP scans identify rogue devices, shadow IT deployments, and unauthorized SIP trunks on enterprise networks.
- Continuous Security Monitoring: Automated scans detect configuration drift and new vulnerabilities as SIP infrastructure evolves.
Conclusion: The Future of SIP Scan and VoIP Security
SIP scan remains a vital practice for VoIP security in 2025. As SIP vulnerabilities persist and attackers grow more sophisticated, automated SIP scanning, integration with security platforms, and advanced analytics are shaping the future. Embracing these tools and best practices is essential for any organization relying on SIP-based communication systems.
Want to level-up your learning? Subscribe now
Subscribe to our newsletter for more tech based insights
FAQ